Ignition Inductive Automation Crack
- Ignition Inductive Automation Crack Update
- Inductive Automation Ignition Software
- Inductive Automation Ignition Maker Edition
- Inductive Automation Ignition
- Ignition Inductive Automation Crack 2019
- Inductive Automation Ignition Manual
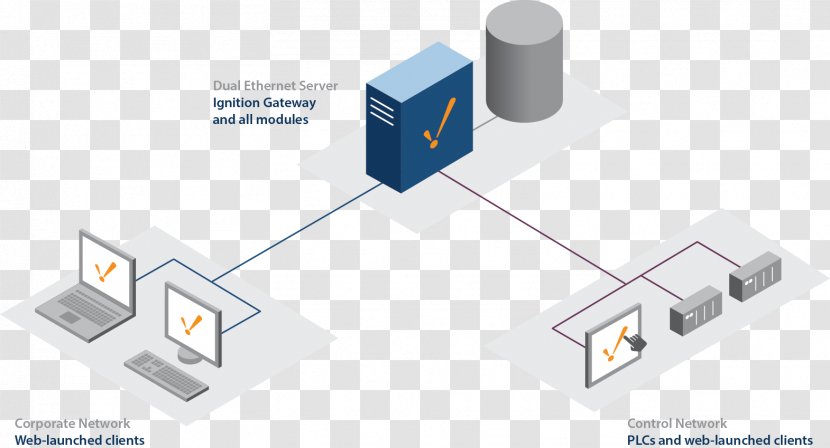
Inductive Automation has 7 repositories available. Follow their code on GitHub. We're a full service automation system integrator. Custom applications such as systems integration, machine retrofits, controls, SCADA, robotics and more. Ignition Certified Integrator. Ignition, by Inductive Automation, is the first worldwide database-centric, 100% cross-platform, web-deployed industrial application platform for.
I have a customer who asked for what I first thought would be a simple query, and after attempting to do it, turns out seems quite hard. I’m hoping that there is a simple solution that I’m overlooking.

They are logging a pressure on a vessel, and they have an alarm at 0.5 psi, but the would like to have a page that allows them to look at some other low points for the day. For example, the want a screen that has a start date and an end date entered on the screen, they also have a pressure value, say 2psi. From this they want to query the history to see how many times they fell below 2psi between the dates. In the database, its quite simple using a query but from ignition there do not seem to be any tools that allow this. I cant query the database directly without knowing what tables to look at, and the dates might span a month (last day of one month to the first day of the next) and that means is will be in two different tables.
I even tried to just pull up a table with all the data between the dates and then try to extract the needed data from the dataset that was generated. I thought this would be the simplest, but I’m finding it hard to query the dataset. I’ve been able to highlight the data with the mapped background function, but I cant seem to find a way to “hide” the other data or pull out the data with highlighted cells.
Ignition Inductive Automation Crack Update
I’m pretty sure someone will have a simple solution and I’ll feel dumb for not thinking of it.
Michael
1. EXECUTIVE SUMMARY
- CVSS v3 9.8
- ATTENTION: Exploitable remotely/low skill level to exploit
- Vendor: Inductive Automation
- Equipment: Ignition
- Vulnerabilities: Missing Authentication for Critical Function, Deserialization of Untrusted Data
Inductive Automation Ignition Software
2. UPDATE INFORMATION
This updated advisory is a follow-up to the original advisory titled ICSA-20-147-01 Inductive Automation Ignition (Update A) that was published June 2, 2020, on the ICS webpage on us-cert.gov.
3. RISK EVALUATION

Successful exploitation of these vulnerabilities could allow an attacker to obtain sensitive information and perform remote code execution with SYSTEM privileges.
4. TECHNICAL DETAILS
4.1 AFFECTED PRODUCTS
The following versions of Inductive Automation Ignition are affected:
- Inductive Automation Ignition 7 Gateway versions prior to 7.9.14
- Inductive Automation Ignition 8 Gateway versions prior to 8.0.10
4.2 VULNERABILITY OVERVIEW
4.2.1 MISSING AUTHENTICATION FOR CRITICAL FUNCTION CWE-306
The affected product lacks proper authentication required to query the server.
CVE-2020-12004 has been assigned to this vulnerability. A CVSS v3 base score of 5.3 has been calculated; the CVSS vector string is (AV:N/AC:L/PR:N/UI:N/S:U/C:L/I:N/A:N).
4.2.2 DESERIALIZATION OF UNTRUSTED DATA CWE-502
The affected product lacks proper validation of user-supplied data, which can result in deserialization of untrusted data.
CVE-2020-10644 has been assigned to this vulnerability. A CVSS v3 base score of 9.8 has been calculated; the CVSS vector string is (AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H).
4.2.3 DESERIALIZATION OF UNTRUSTED DATA CWE-502
The affected product is vulnerable to the handling of serialized data. The issue results from the lack of proper validation of user-supplied data, which can result in deserialization of untrusted data.
CVE-2020-12000 has been assigned to this vulnerability. A CVSS v3 base score of 9.8 has been calculated; the CVSS vector string is (AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H).

--------- Begin Update B Part 1 of 2 ---------
4.2.4 MISSING AUTHENTICATION FOR CRITICAL FUNCTION CWE-306
Sensitive information can be obtained through the handling of serialized data. The issue results from the lack of proper authentication required to query the server.
Inductive Automation Ignition Maker Edition
CVE-2020-14479 has been assigned to this vulnerability. A CVSS v3 base score of 5.3 has been calculated; the CVSS vector string is (AV:N/AC:L/PR:N/UI:N/S:U/C:L/I:N/A:N).
--------- End Update B Part 1 of 2 ---------
4.3 BACKGROUND
- CRITICAL INFRASTRUCTURE SECTORS: Critical Manufacturing, Energy, Information Technology
- COUNTRIES/AREAS DEPLOYED: United States
- COMPANY HEADQUARTERS LOCATION: United States
4.4 RESEARCHER
Inductive Automation Ignition
Pedro Ribeiro, Radek Domanski, Chris Anastasio (muffin), and Steven Seeley (mr_me) working with Trend Micro’s Zero Day Initiative reported these vulnerabilities to CISA.
Ignition Inductive Automation Crack 2019
5. MITIGATIONS
Inductive Automation recommends upgrading the Ignition software to v8.0.10
For those running v7.9.x, it is recommended to upgrade the Ignition software to v7.9.14
--------- Begin Update B Part 2 of 2 ---------
Please note CVE-2020-14479 does not have a fix in place. Induction Automation plans to correct this vulnerability in future product versions.
It is recommended to restrict interaction with the service to trusted machines. Only clients and servers with a legitimate procedural relationship should be permitted to communicate with the service. This can be done in various ways, most notably with firewall rules/allow listing.
For more information regarding software and patches, please refer to the specified version in Inductive Automation’s release notes.
--------- End Update B Part 2 of 2 ---------
CISA recommends users take defensive measures to minimize the risk of exploitation of this vulnerability. Specifically, users should:
- Minimize network exposure for all control system devices and/or systems, and ensure that they are not accessible from the Internet.
- Locate control system networks and remote devices behind firewalls, and isolate them from the business network.
- When remote access is required, use secure methods, such as Virtual Private Networks (VPNs), recognizing that VPNs may have vulnerabilities and should be updated to the most current version available. Also recognize that VPN is only as secure as the connected devices.
CISA reminds organizations to perform proper impact analysis and risk assessment prior to deploying defensive measures.
CISA also provides a section for control systems security recommended practices on the ICS webpage on us-cert.gov. Several recommended practices are available for reading and download, including Improving Industrial Control Systems Cybersecurity with Defense-in-Depth Strategies.
Additional mitigation guidance and recommended practices are publicly available on the ICS webpage on us-cert.gov in the Technical Information Paper, ICS-TIP-12-146-01B--Targeted Cyber Intrusion Detection and Mitigation Strategies.
Organizations observing any suspected malicious activity should follow their established internal procedures and report their findings to CISA for tracking and correlation against other incidents.
No known public exploits specifically target these vulnerabilities.
Contact Information
For any questions related to this report, please contact the CISA at:
Email: CISAservicedesk@cisa.dhs.gov
Toll Free: 1-888-282-0870
For industrial control systems cybersecurity information: https://us-cert.cisa.gov/ics
or incident reporting: https://us-cert.cisa.gov/report
CISA continuously strives to improve its products and services. You can help by choosing one of the links below to provide feedback about this product.
Inductive Automation Ignition Manual
This product is provided subject to this Notification and this Privacy & Use policy.
Please share your thoughts.
We recently updated our anonymous product survey; we'd welcome your feedback.